Lepide Auditor Suite is a complete system to audit, control and manage your IT infrastructure. There are 3 type of companies. Small businesses usually don’t have resources to even think about something as essential as keeping audit log for all IT services. Medium sized companies have a need of large enterprises, but they lack the budget of bigger organizations. They have to follow the same procedures and the same rules. Unfortunately, their budget does not have a place for such solutions. Big companies don’t have a place for an error. They have to be prepared for attacks from external and internal sources. The more employs you have, the more likely there is an individual who will try to gain unauthorized information. To keep up with such scenarios you have to have the right tools. Lepide analyzed most common issues IT faced and created one of the best IT tools. Lepide Auditor features solutions the problems IT faces. No matter the company size, the problem is there. The question is what you will do to prevent and improve the audit trail in case you face an incident. Even better, what will you do to prevent an incident?
Depending on the size or type of the company, you may be objected to IT Audit. I know from the first hand how difficult it can be to satisfy all the requirements, especially if your department is smaller in size and you can’t afford good software solutions.
Let’s take a look how Lepide will help to minimize our IT problems. Including IT audit. Lepide Auditor suite is a collection of a unified Centralized platform to audit MS Active Directory, MS File Servers, MS Active Directory and Group Policy, MS Exchange Server, MS Share Point Server and MS SQL Servers.
Lepide Auditor Suite users are impressed by the simple installation and easy to use interface. Installation takes only a minute or so, and configuration is as simple as pressing next button.
For each service that you wish to monitor, you have to add a server and credentials. Once that is complete, you can sit back and wait for Lepide Auditor to start a collection process.
Lepide Auditor Review – Why you will love it
When you install and configure Lepide Auditor, you gain visibility to:
- Permission Analysis
- Threshold alerting
- Advanced search
Lepide Auditor will help you keep your environment secure by supporting the following IT services:
- MS Group Policy
- MS Active Directory
- MS Exchange
- MS SQL Server
- File Server
- MS Sharepoint
In every organization you have to keep track of your user activity, you never know when you have a potential hacker among your staff. Don’t think that because a user works in the warehouse, that he doesn’t know how to exploit the system. You also have to know what is happening to your files and folders and who is accessing them. What if you could keep a log about deletions and modifications? Once you start securing your IT, you have to keep an eye on effective permissions. Don’t forget about changes to permissions of any file and folder. Also, you need to have a system that will alert you in real time of the problems. By automating report delivery to your inbox, you ensure that you always have the current information.
Changes in log files are one of the first signs that the hacker has penetrated your system. Lepide Auditor has a system which protects log integrity.
Increased CPU and Memory usage could be a sign that something is wrong and that data is being leaked for example. Lepide Auditor has a monitoring system built in which will help with such scenarios. By using Lepide Auditor Monitoring system, you may also improve your user’s experience. You will know when the systems are being slow as you will receive email alerts in real-time. Because you will become pro-active, users will love you.
While having the right tools for the right job is excellent, what is even better is that you have access to around 270 pre/built reports, all focusing on security.
You can grant access to a web-based console where you can delegate and revoke access to reports to a user with appropriate access. That way you can employ least privilege access. Often this kind of reporting comes handy for the auditors, internal or external.
There are many organizations which are bound by compliance. There are many standards, and Lepide Auditor supports all – FISMA, GLBA, HIPPA, PCI, SAS and SOX.
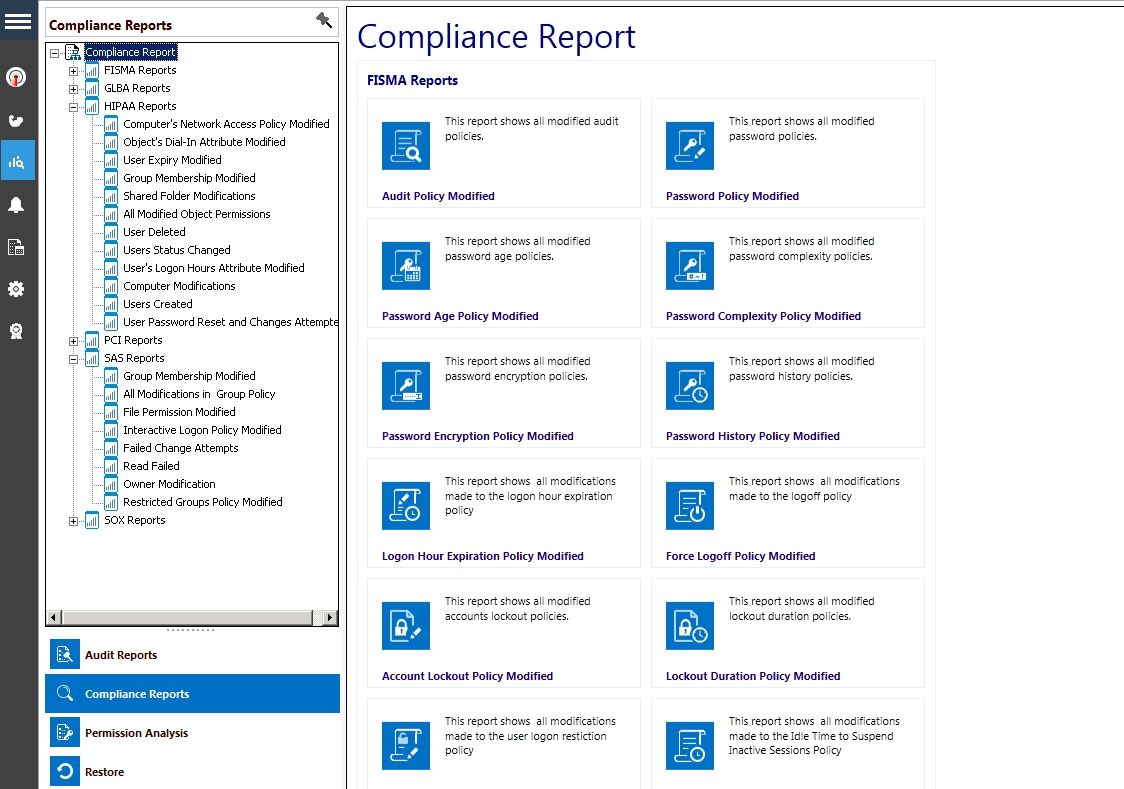
Monitor policy changes and your infrastructure
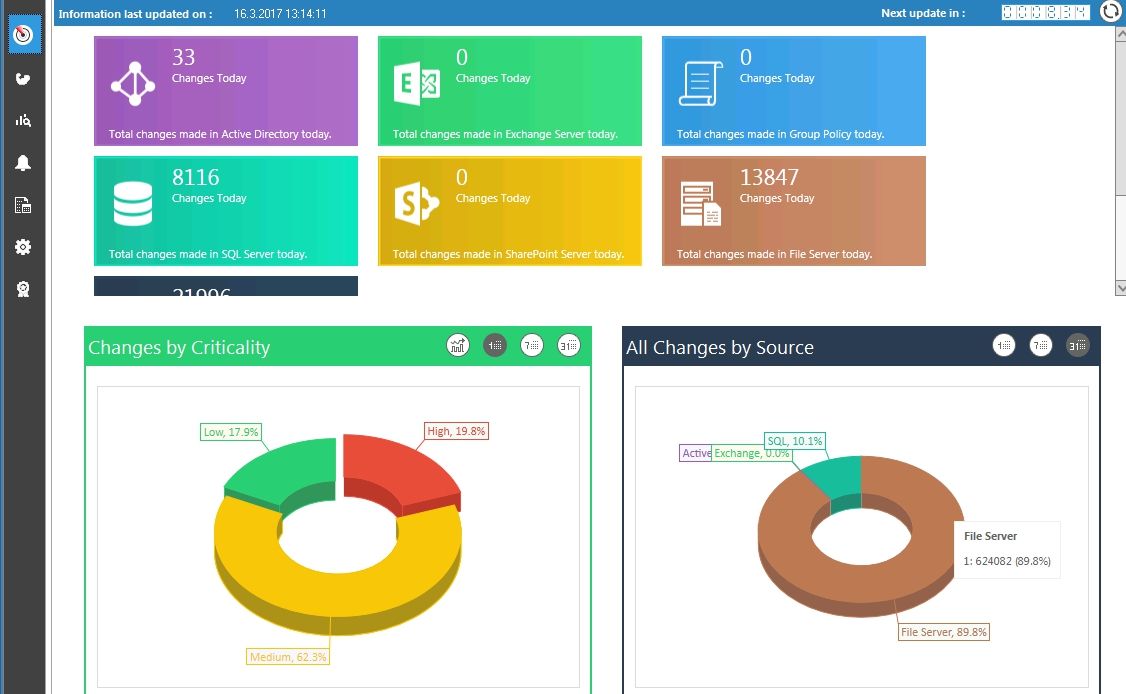
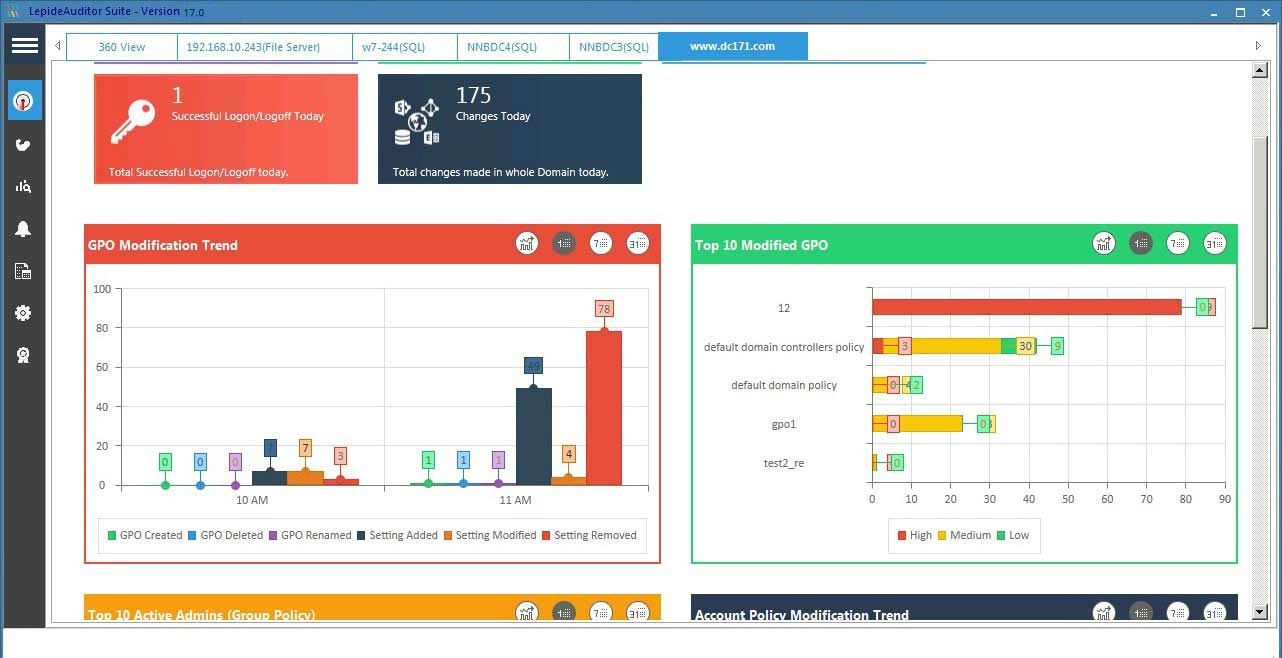
Did I mention that Lepide Auditor has a smooth interface? Once you start using it, you will love it. It features a 360 View where you can see in a second how many changes occurred on each service.
360 View and Server Monitoring
Let’s say that you are interested in changes in MS Exchange. All you have to do is to click on the Exchange Server area, and you will drill down to information that you require easily. You can also look at the server which is being monitored and spot problems by looking at the CPU and RAM consumption, running services, etc…
Boost your security like a ninja
Know what’s happening with Active Directory and Group Policy
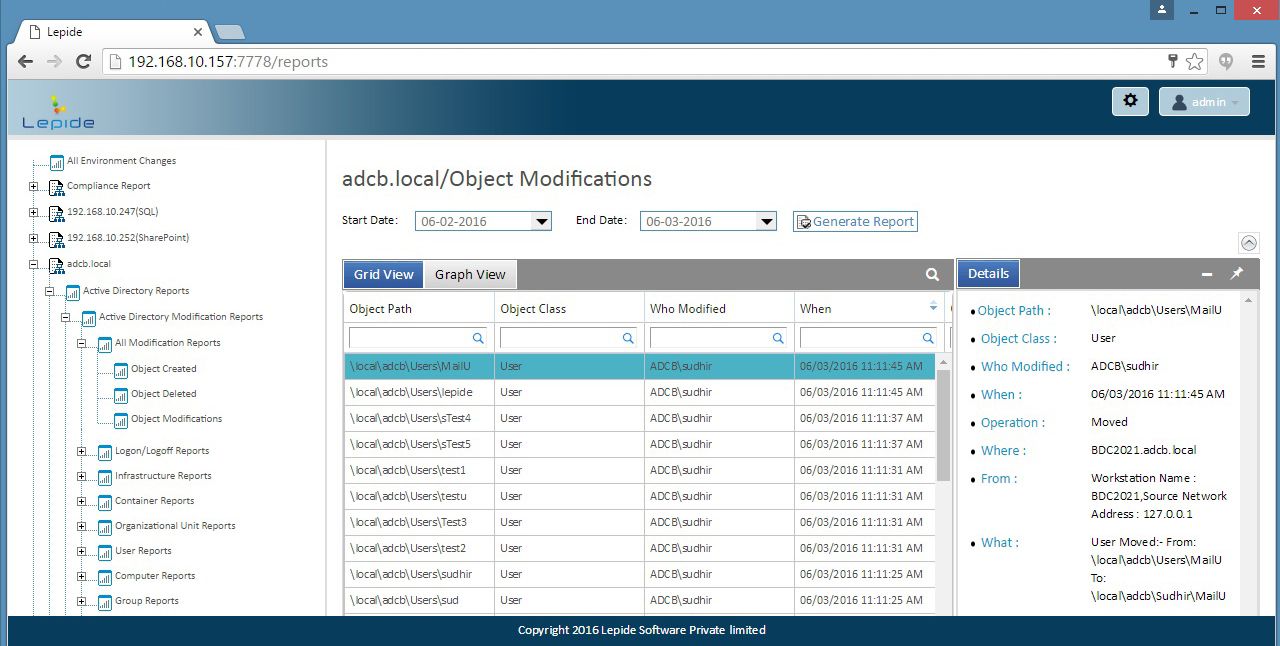
Active Directory is one of the main pillars of IT infrastructure. By tinkering with group permissions, you can gain access to the company most kept secrets. At the same time, by doing small changes to AD or group policy, you can do extensive damage. With Lepide Auditor, you will know who modified AD and what was changed. Similarly, you will know who changed any setting in GP, who changed password policy, who revised security policy, etc…
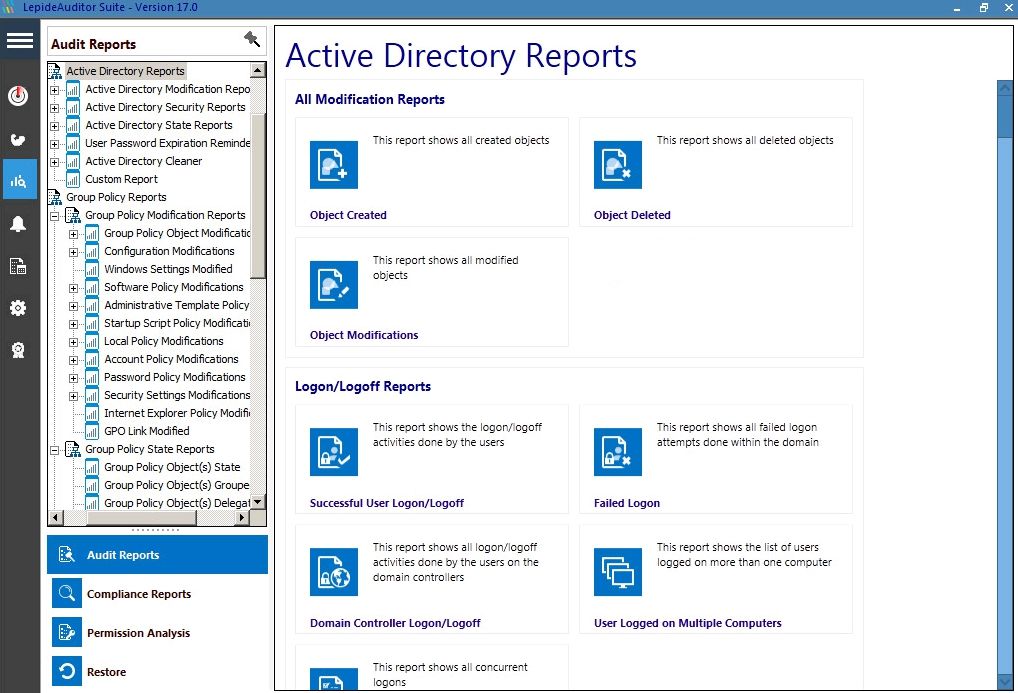
What can you do to make your Active Directory more secure and in good shape? Lepide Auditor is made for Active Directory and Group Policy. To improve security, there are many reports. All Permissions to an Object, Permission modifications, Group Policy modifications, User And computer policy configuration, Local Policy change. To make your AD and GP in shape, you can run reports. To maintain AD, you can run reports like All Empty Organization Units, List All Groups without members, OU Created, Computer created. You can also monitor Infrastructure changes like DNS Zone modifications, Schema Modifications, Trust modifications, Domain Controller modifications. For every aspect, you will find a report.
One of the many features you will like is a way to see not only what was changed, but also what was it changed from. That way you see a change and original value.
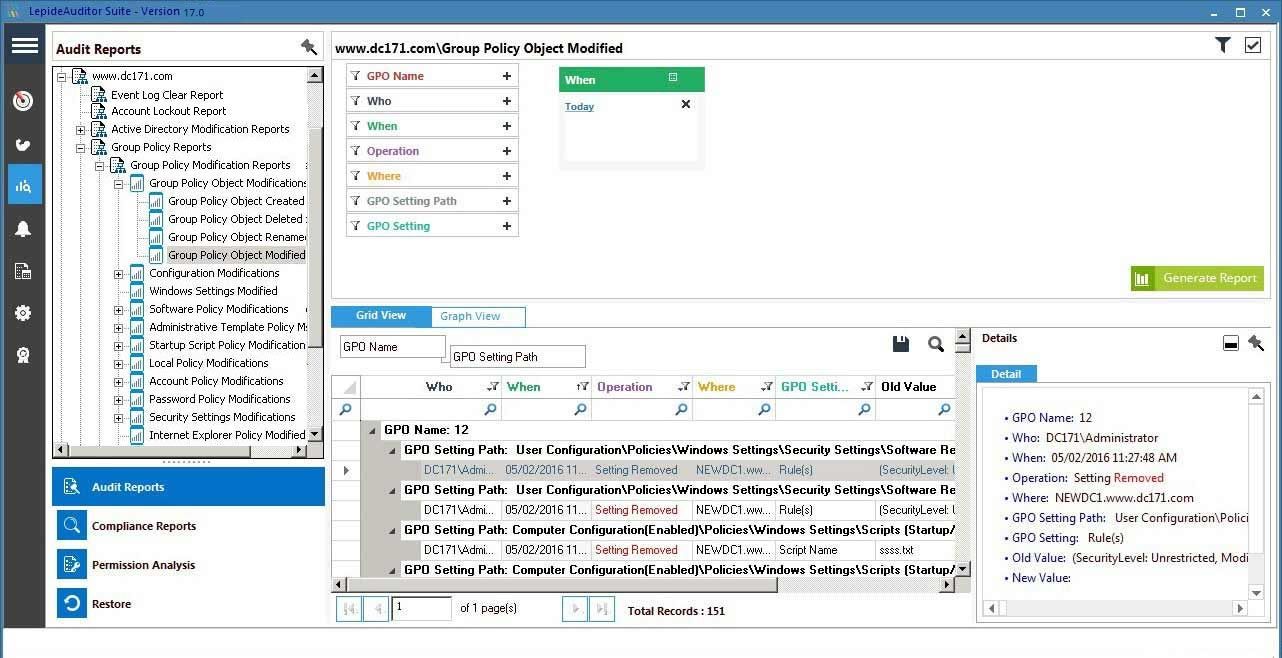
Often when you stumble on a change you would like to revisit, you would give everything to revert that change quickly. Lepide Auditor keeps a backup of all the changes, and you can quickly revert to the original setting. How awesome is that?
Sometimes all you want to do is to get an overview of Group Policy changes. You can quickly look at Group Policy change trends on the Group Policy console. You can see who made the most changes and can easily spot any anomalies in the timeline. You can drill down and get an even better overview of the changes.
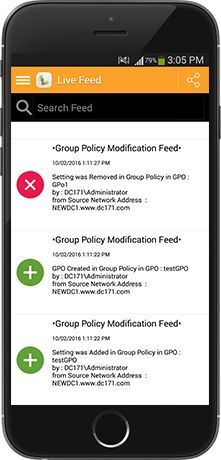
Lepide also features mobile application. It is a perfect tool, to monitor Active Directory and Group Policy changes while traveling or when you are not at your desk. That way, you can easily keep an eye on the changes.
That way, you can easily keep an eye on the changes.
File Server audit tool
I wish I had this tool at my disposal several years ago when we had a mole in the company. We had an unusual situation. We were designing retail catalogs with super deals. They were sent to the print shop at midnight. Next day in the morning catalogs were sent to the delivery company. Competition didn’t have time to respond quickly. But magically, competition knew our prices and our product selection. They usually scheduled catalogs on the same day with the same products and even better prices.
We never found the mole, but with this kind of tool, I know it would be very simple to locate the person leaking information. You see, one of the features, which I like personally, is the ability to know which files were copied. For the company assets, you need this information.
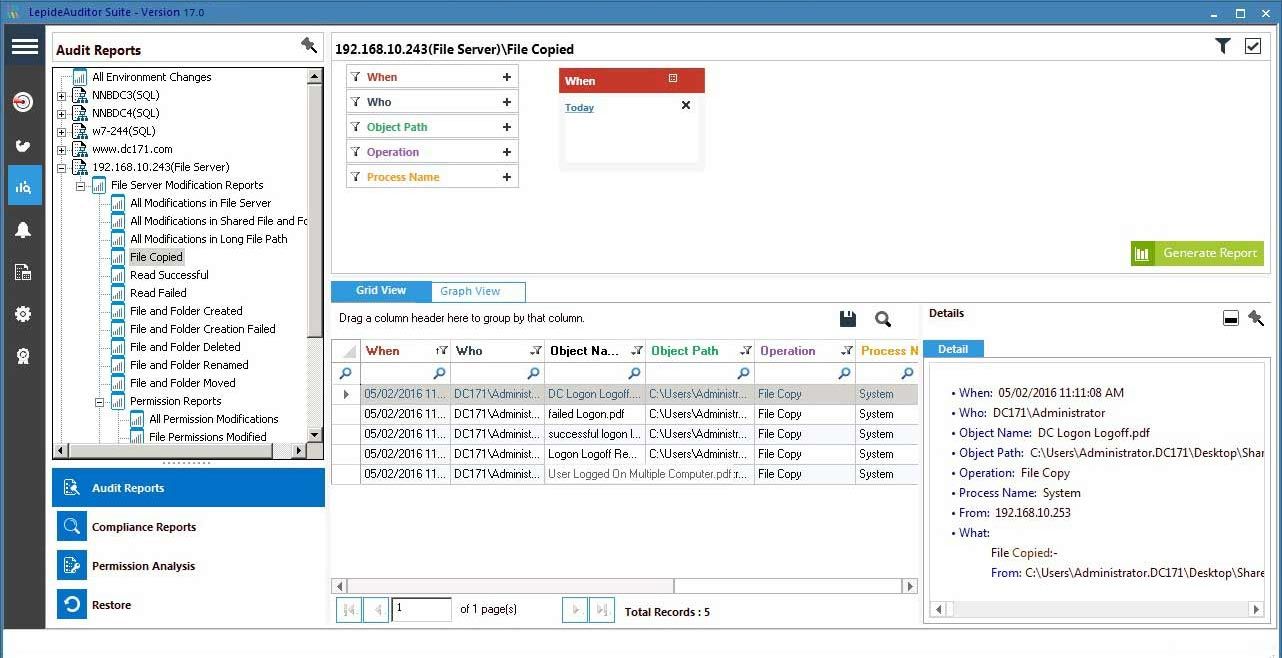
Besides to file copy reports, you can gain insights to file modifications on the server, changes in shared file and folder, successful read files, created files and folders, deleted files and folders, renamed files and folders, etc… The list is so extensive you can cover all the trails you may need. Also, what I also like is the ability to review the permission changes on the file server. Where this comes handy is when you have a folder that you have to protect. You can review all the changes that happened in a certain period quickly. You can instantly spot permission changes.
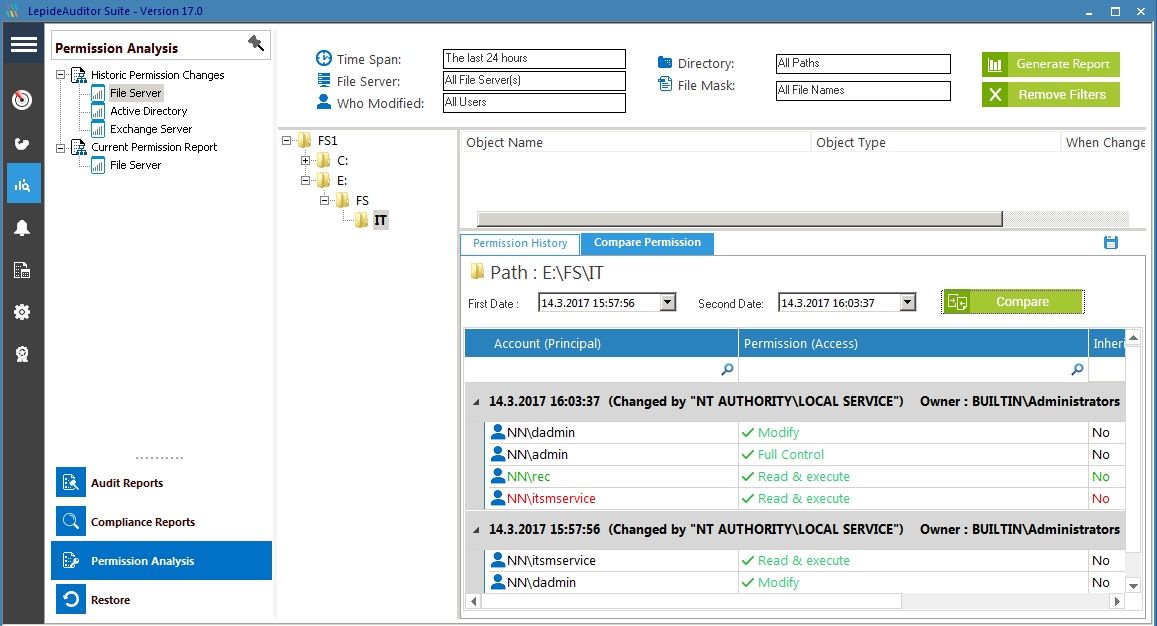
Group memberships are one of the easiest ways for a user to get a membership to a folder which he does not belong. IT Technician can also make a mistake with the access. Even worse, IT Technician can add a user he is collaborating with, to the access list. If you don’t review Group membership that often, you can miss anomaly like this. By setting up alerts for group membership changes, you will receive an immediate alert and will be able to prevent a leak.
Exchange Audit Tool
As soon as you connect your MS Exchange, you have the ability to get information from the user accounts. When IT department is a team of more than two people, there is a chance of unauthorized access to the data. Trust me, people are interesting. Even though you believe in your team, there may come a day when some of them, will try to gain access to another user mailbox. In my previous job, my boss, IT Manager, was in love with a secretary. He was afraid to tell her his feelings. I don’t know why, but he used his access to check her email. Her friend sent her an email with reading confirmation request. When he opened this email, email request got confirmed with his credentials – this was Lotus Notes and friend received read confirmation from this guy. Yes, she told this to the secretary. I don’t know how, but he was able to persuade her, that this was a server error.
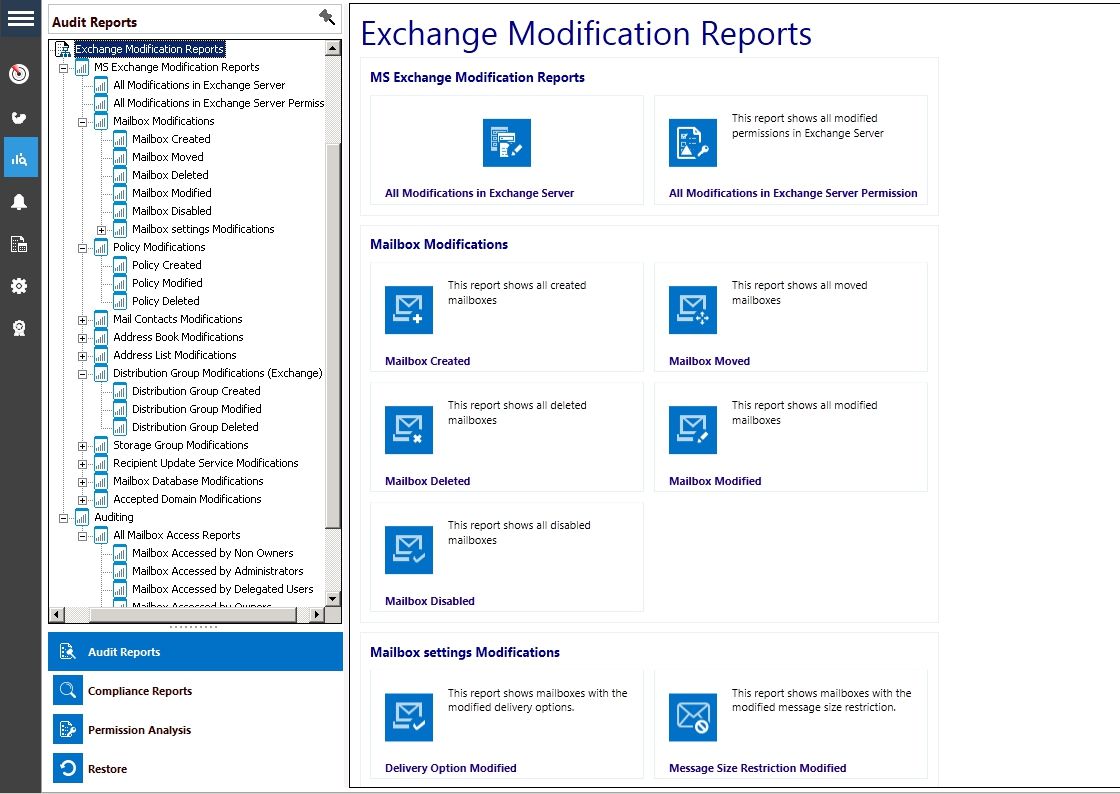
This is just a small example how the system can be easily abused. As soon as you are a team, you need a system to spot problematic behavior.
Lepide Active Directory Cleaner
If I have to choose a functionality that I like the most, I will select Lepide Active Directory Cleaner. It’s the perfect tool to proactively monitor and protect your active directory from the ghost objects. By ghost objects, I mean users and computers that were supposed to be disabled long time ago but were not due to a mishap in HR and or IT procedure. HR should have notified IT about users who no longer work in the company. At the same time, IT should do monthly checks about active users. Proactively. But without proper tools, this is hard to do. Lepide Active Directory Cleaner is all about cleaning and preventing users and computers no longer present with the company accessing our infrastructure.
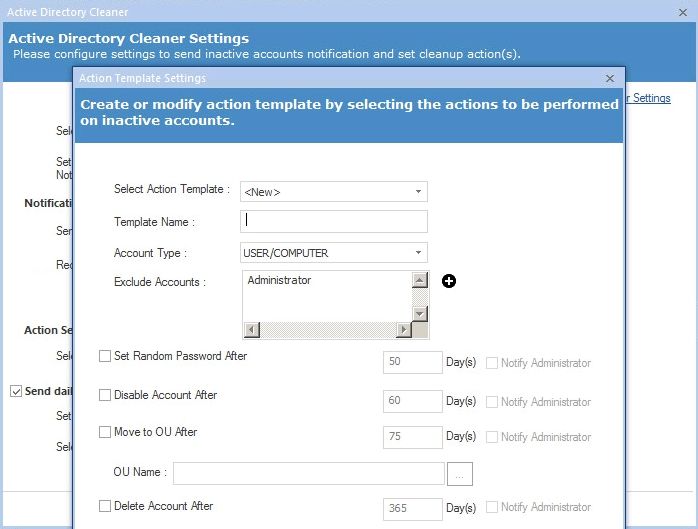
The way this works is simple. We set a template with rules. For example, take a look at our AD, find users that are inactive for X days. What we should after 50 days is that we set a random password. After 60 days of inactivity, the same account will be disabled. Since its very likely that this account is not in use after 75 days of inactivity we should move it to an Organization Unit which we use for disabled accounts. We can also set a rule to delete the user after 365 days for example automatically. Just in case we forget. Please note that you can set custom time policy according to the way you have set your domain policy. From the example, you can see how useful is this tool.
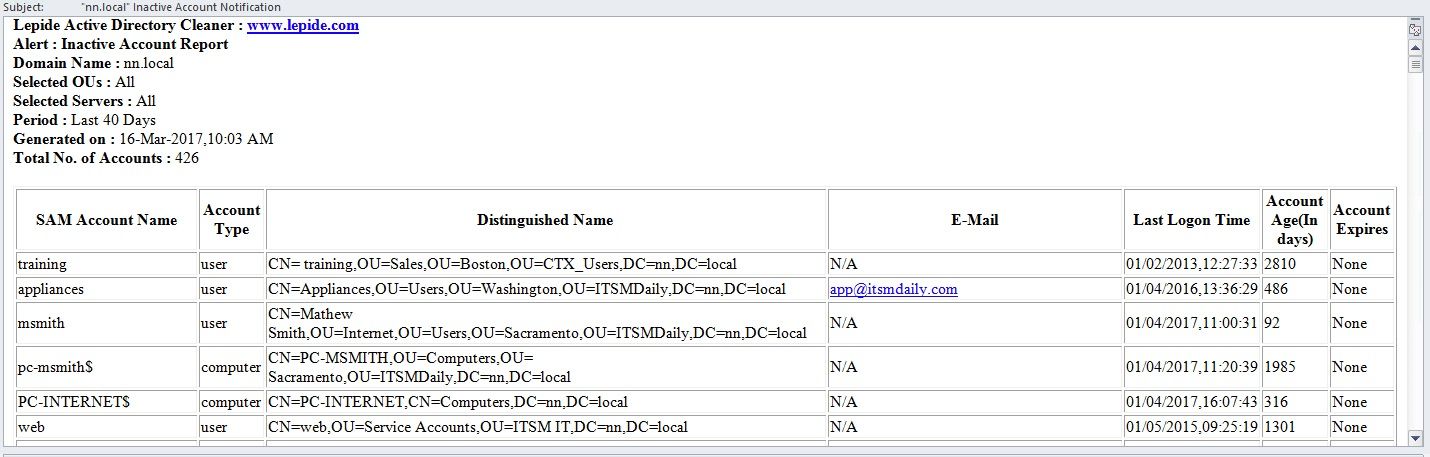
Inactive Account Notification
I often mention examples of our HR, which forgets to notify IT that people have left the company. It does not matter if they got sacked or they resigned with good intentions. The fact is that they are a threat to the enterprise. They know the system, they know the location of documents. They know which mapping or a service they have to use to gain access to the files shared with employees.
Lepide has a great feature called Inactive Account Notification. What Inactive Account Notification does, is not revolutionary, but it helps. Boy, it helps. It will send you an email with a list of all accounts which are inactive. It will look at the selected domain, under selected OUs, It will watch the X period (you set the number of days of account inactivity so that it aligns with your security policy). It will then, send you emails with listed inactive accounts. What I like to do with this email is that I point it to our service desk email and set up a rule that the right group is assigned to the ticket. Guys then review the accounts and close one in case it is not yet disabled. Perfect pro-active job for audit.
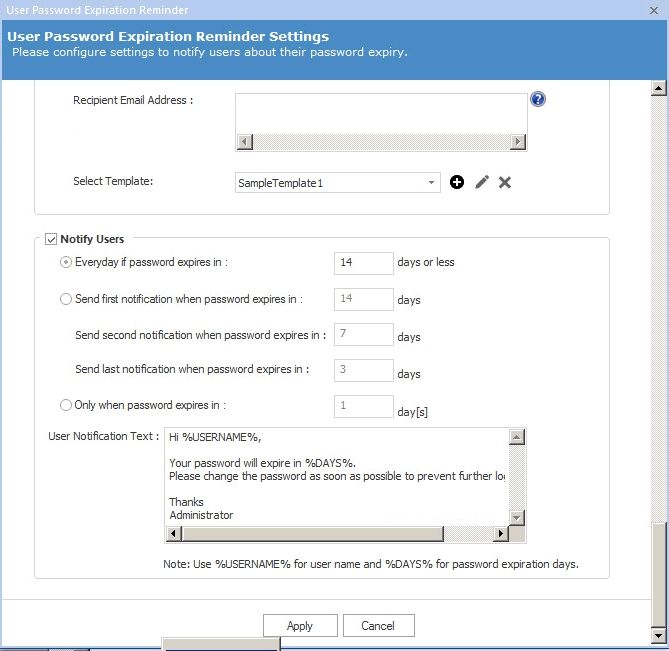
Password Expiration Reminder
As a bonus, Lepide Auditor includes Password Expiration Reminder tool. Similar tools sell separately. Lepide chose to include it part of the package which is great. You see, password related problems are very high on the helpdesk most requested list. By implementing password expiration into your organization, you will lower password related issues. In turn, you will decrease the number of tickets.
You can define when to notify users – every day when it reaches the threshold, or you can send more refined policy like first mail is sent when a password expires in X days, second notification when the password expires in X days and the last notification when the password expires in X days. You can also opt to send only one email when the password expires in X days.
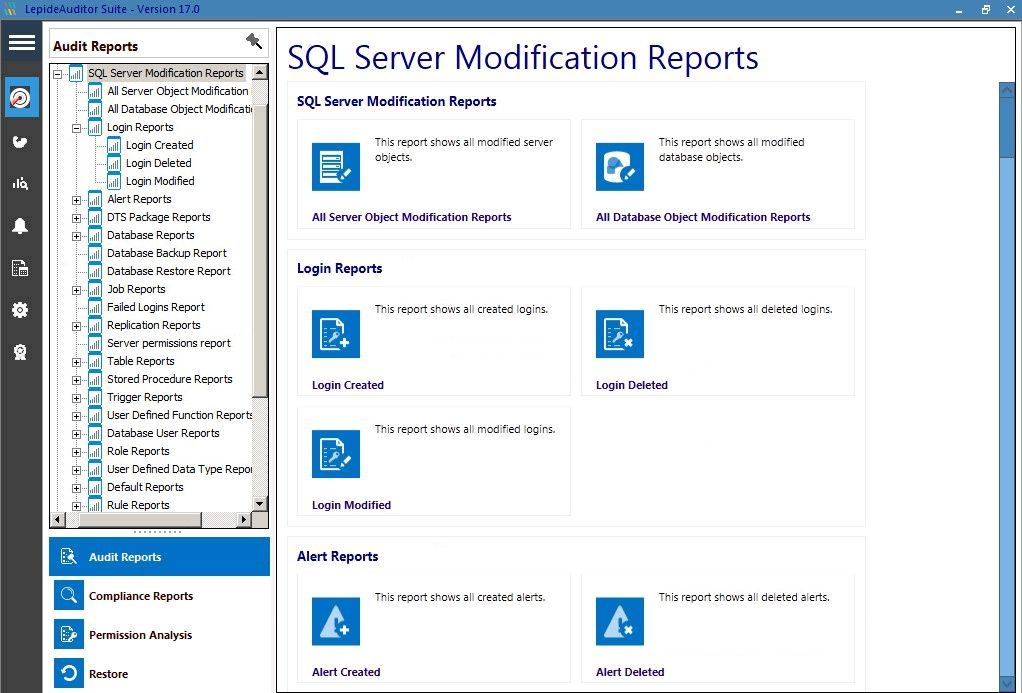
MS SQL Audit tool
On the last check, auditor asked me if we keep logs of users accessing the database. Good question. I know many small companies don’t have SQL Administrator in their IT Team. In such organizations, SQL is usually managed by the same company that sold the ERP system. The question auditor asks no matter the company is size is: who accessed what data, who obtained data when and who authorized that. This is just a fundamental question that many IT Managers have to face when they meet with Auditors.
This is where smart people have the advantage. When you use the right software, you will have to answers to all questions from the auditors. Lepide Auditor Suite will help you with SQL audits.
There are so many built-in reports that you will hardly find one missing. For example, SQL Login reports (Login Created, Login Deleted, and Login Modified), Database backup report, Database restore report, Replication report, Role reports, Server Permission report….
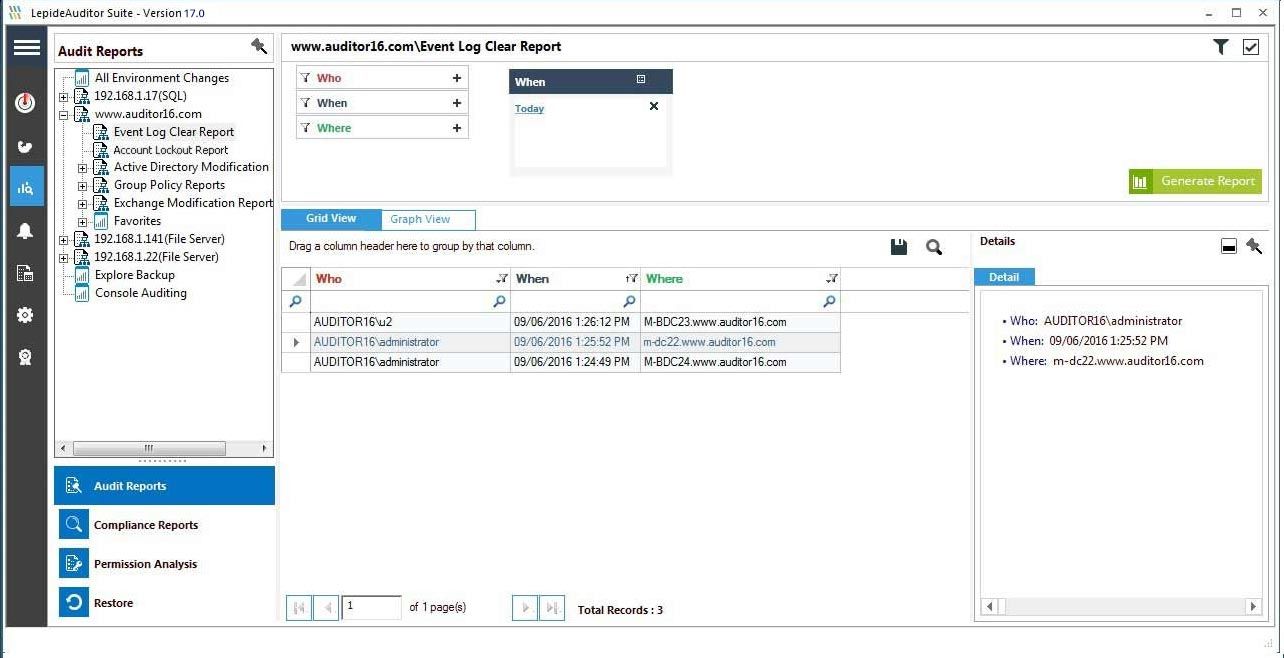
Event Log – Security assets no. 1
The Event log is vital. Usually, we don’t think of it. But Event log keeps track of every action happening in our system. From Login to permission changes. When all the systems are running, we don’t even think about it, and that is most of the time. But when we have problems either with the hardware, software or security, first thing we have to remember is to check the Event log. All the events and actions are listed in the event log, including security and access. One of the first actions attacker does, is a procedure to cover his or her tracks. Clearing event log is easy. To protect and prevent this kind of anomalies, we can use Lepide Auditor to notify us on Log Clear Events. We will know who, when and where the attacker cleared event log.
Backup and restore
What happens when you discover that an object has been deleted in AD? You can start a procedure to restore the object from the backup if you have one. But what I think is another neat feature of Lepide Auditor is the ability to backup and restore objects. A procedure is straightforward and quick.
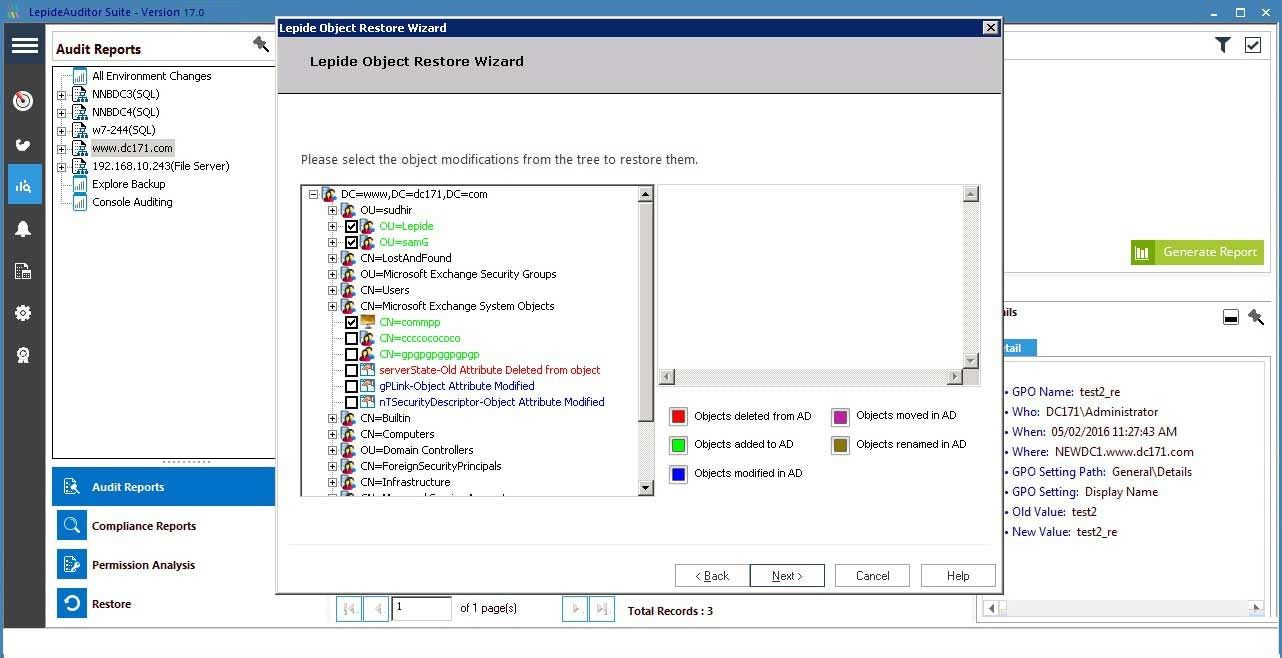
As a general disaster recovery rule, you should always have the backup stored in 3 locations. Lepide Auditor may save you one day, you never know, when you may need to restore from Lepide.
Conclusion
For every system review, where you typically run a report, you can also schedule reports via emails. That way we can automate already a perfect system to make our system more secure. What I love about Lepide Auditor is that it covers all our company needs for security. It goes even further by adding features that are sold separately in many cases. It secures Group Policy and Active Directory – two of the most important pillars of most IT systems. You may not think about it, but if it prevents unauthorized group modification. It will defend you from unauthorized access to the folders. Lepide Auditor will secure your files as it will monitor permissions and even advanced functions like file copy. Imagine NSA having such system in place, Snowden would not happen as the copy action would trigger alerts in the HQ.
Auditors also like to know that you have control over SQL. With Lepide Auditor, you become a SQL information master. You know who, when, what. This is not only useful if you have in-house SQL team, but is also beneficial if external ERP team supports SQL.
Besides, you will have a complete Event log protection, even better, you will receive an alert, if a user tries to delete it.
It does not matter if HR is notifying you the way it should. I mean, I would like to live in the environment with perfect scenarios, but life is life, and it’s better that we accept the challenge and make the most of the situation. By using Password Expiration Reminder, you don’t have to rely on HR department anymore exclusively. Also, you can also audit MS Exchange and MS Sharepoint with the same simplicity you find across the product line. I think this one of the best audit tools for Microsoft environment.

Leave a Reply